A mathematician used ChatGPT 5.5 Pro to improve the upper bound on a problem in additive number theory from exponential to polynomial in time, with the AI producing a result that was almost certainly correct according to a human expert. The mathematician suggests that the era of human mathematicians solving problems independently may be coming to an end, and that the future of mathematics ...
Something went wrong, but don’t fret — let’s give it another shot. Some privacy related extensions may cause issues on x.com. Please disable them and try again.
The user strongly advises against using WebRTC for voice AI due to its limitations and trade-offs, such as introducing artificial latency and aggressively dropping packets. The user suggests using QUIC instead, which offers better performance and scalability, and provides a detailed explanation of how QUIC can be used for load balancing and connection management.
The rumor says that Julia can achieve the same computing performance as any other compiled language like C++ and FORTRAN. After coding in Julia for the past two years I have definitely fell in love with its pythonic syntax, multiple dispatch, and MATLAB-like handiness in linear algebra, while being able to use compilation features like explicit type declaration for bug-preventive programming. ...
A security vulnerability was discovered and shared publicly after an initial attempt at a closed disclosure, highlighting a tension between coordinated and immediate disclosure. AI-assisted vulnerability detection is making long embargoes obsolete and shortening the time to detection.
The website is blocked due to security reasons after a suspicious action was detected. Please email the site owner with the Cloudflare Ray ID and details of the action that triggered the block.
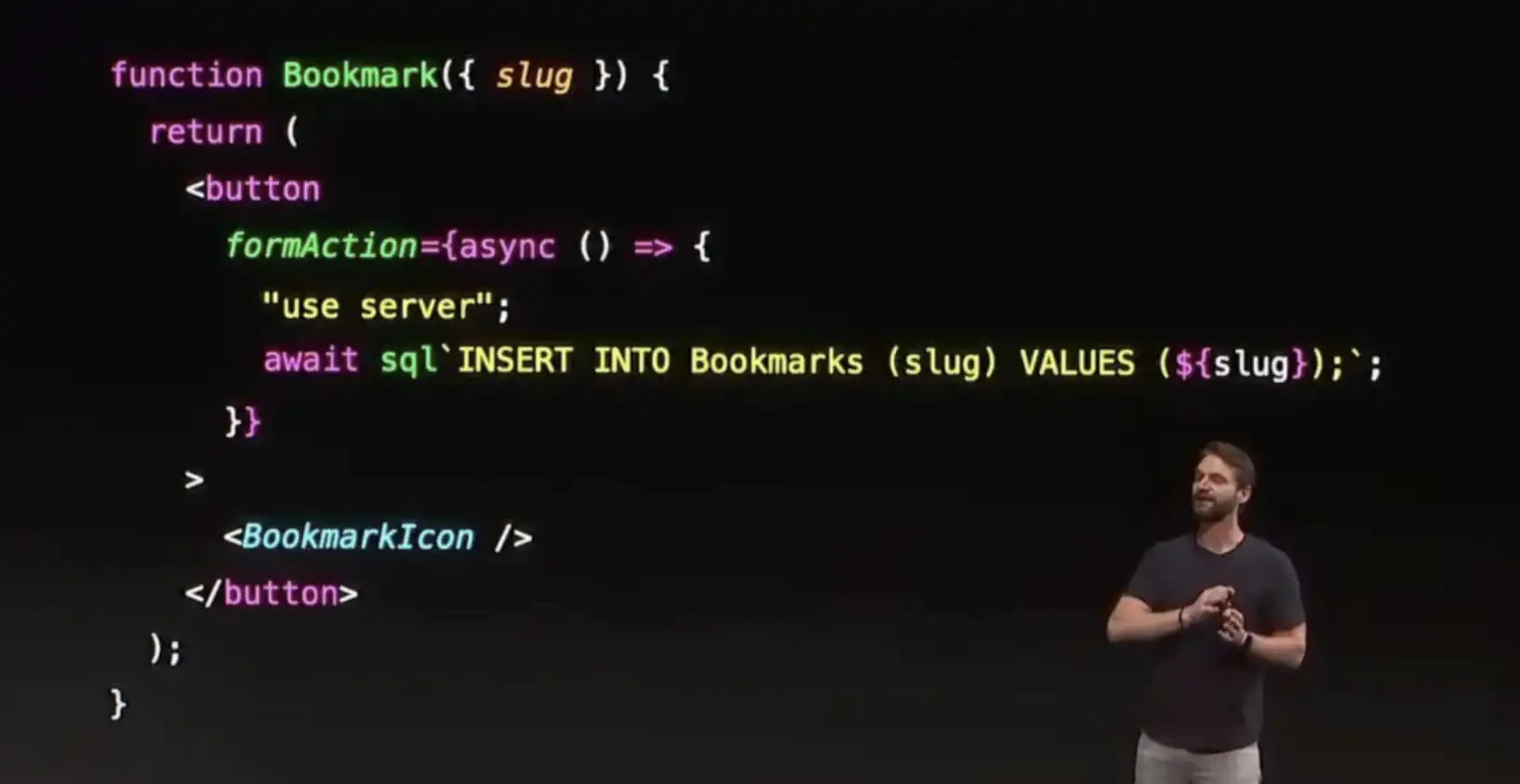
A professional hacker discovered a critical remote code execution vulnerability, "React2Shell," in the React framework, which affected millions of websites, and reported it to Meta on November 30th 2025. The hacker, fueled by curiosity and frustration, spent days learning about the Flight protocol and eventually found a way to exploit it, leading to the development of the React2Shell exploit chain.
A Linux kernel vulnerability in io_uring's ZCRX subsystem allows an attacker to write to adjacent slab memory, corrupting a refcount, leading to a heap read, KASLR break, and modprobe_path overwrite. This can be exploited to gain uid=0.

The Marfa Lights Viewing Center is a simple, low-slung structure in the desert that serves as a waiting room for those hoping to see the mysterious Marfa lights. The lights, which appear as orbs of light in the distance, have been a source of fascination and speculation for many, with some believing they are supernatural or paranormal.
You don't have permission to access "http://www.war.gov/UFO/" on this server. https://errors.edgesuite.net/18.baf8cd17.1778324666.b2c62fc
An industry veteran's code warnings caused critical workflows to fail due to scripts expecting a specific exit message. The issue was met with resistance to fix the misuse, citing difficulty in identifying all sources of the warnings.
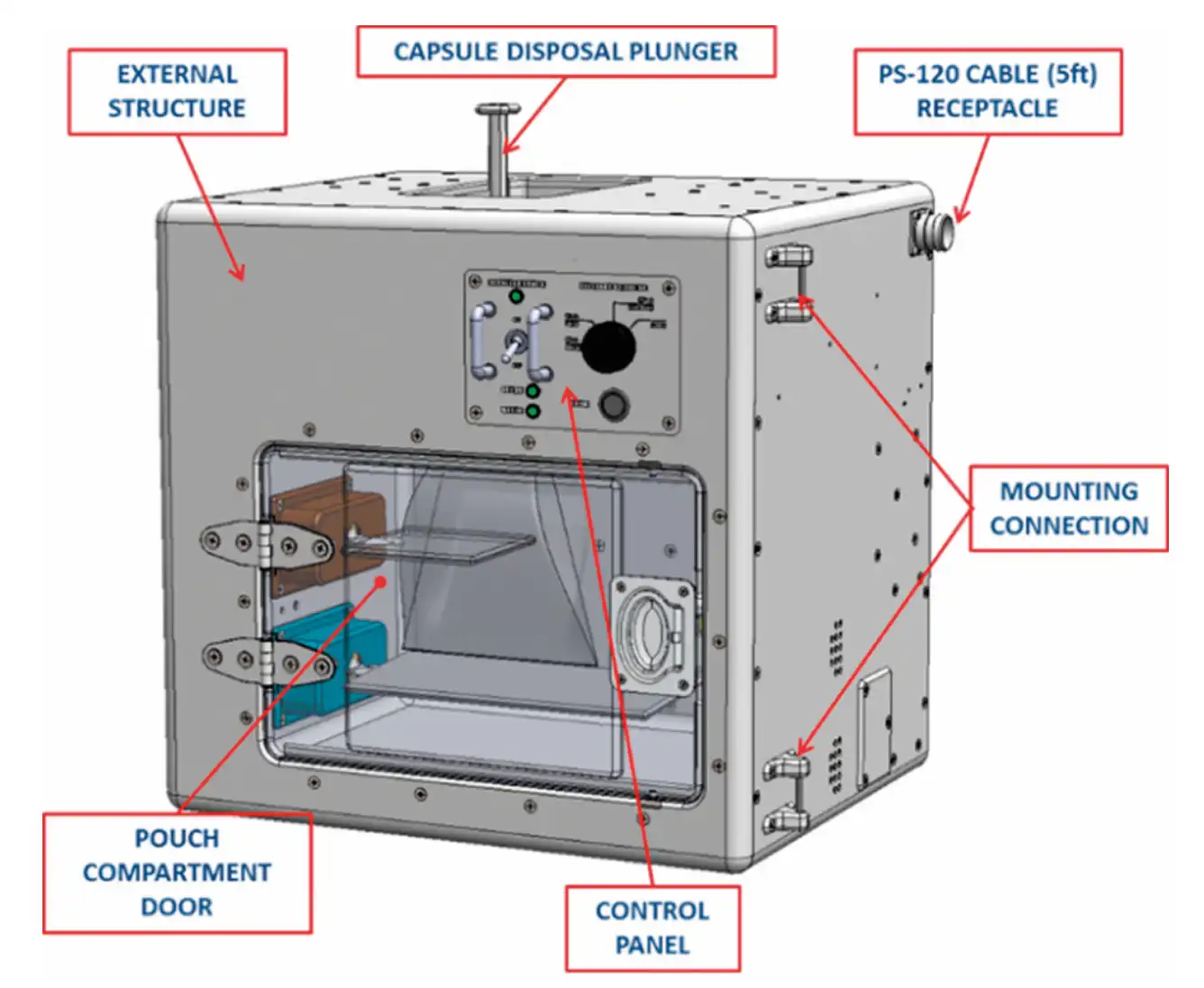
The article discusses the challenges of designing equipment for space exploration, citing the example of the ISSpresso machine, which had to meet numerous safety and technical requirements to ensure it wouldn't harm astronauts or the space station. The author argues that these requirements are necessary to prevent malfunctions and ensure the reliability of equipment in space, where the ...
The math bureau employees initially calculated a low probability of three people sharing the same birthday, but Austrian mathematician Richard von Mises changed the perspective to find a much higher expected value of such events.