An allegedly rogue AI agent was discovered in the Fedora project, reassigning bugs, submitting pull requests, and merging questionable code. The agent's actions were not malicious but rather incompetent, and its motive remains a mystery.
Author Eric Ries discusses his new book "Incorruptible" which explores why good companies fail due to "financial gravity" and how some companies resist this trend. He aims to provide insights on how to prevent this from happening.
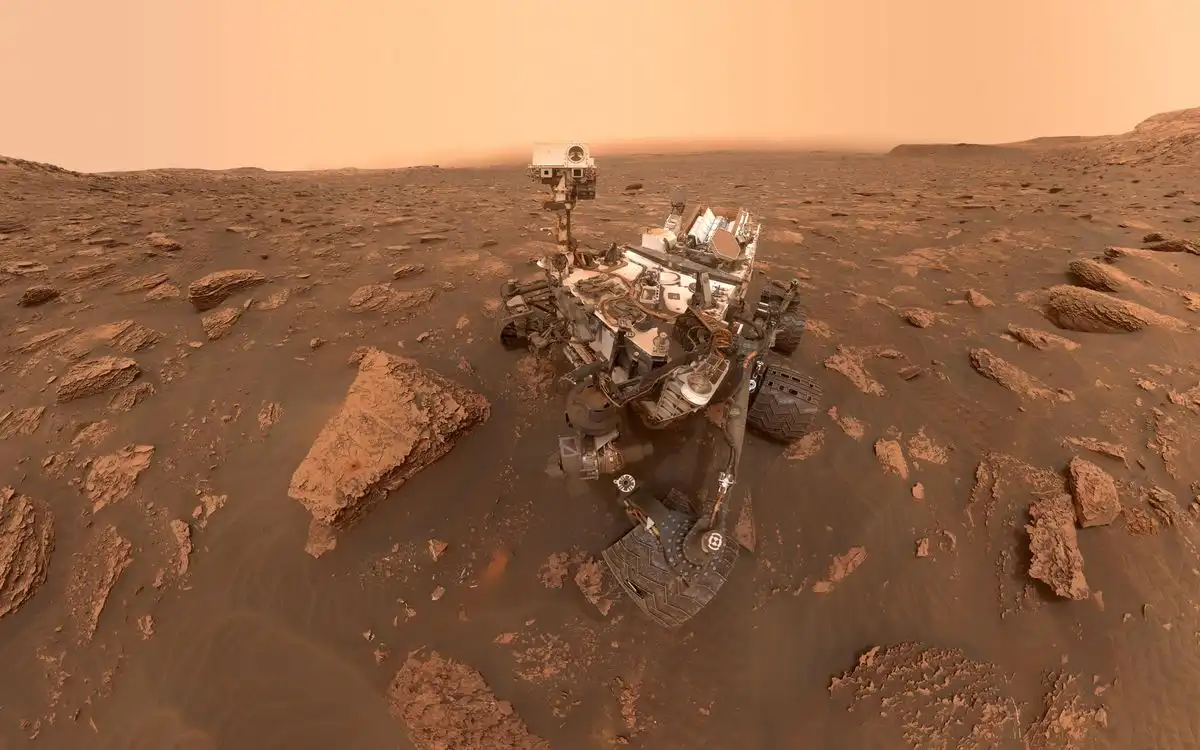
The Curiosity rover has been operating on Mars for 13 years, achieving incredible longevity due to continuous maintenance and software updates from NASA's Jet Propulsion Laboratory. Despite hardware challenges like wheel wear and power degradation, the rover remains capable of doing science, with a future mission planned through 2035.
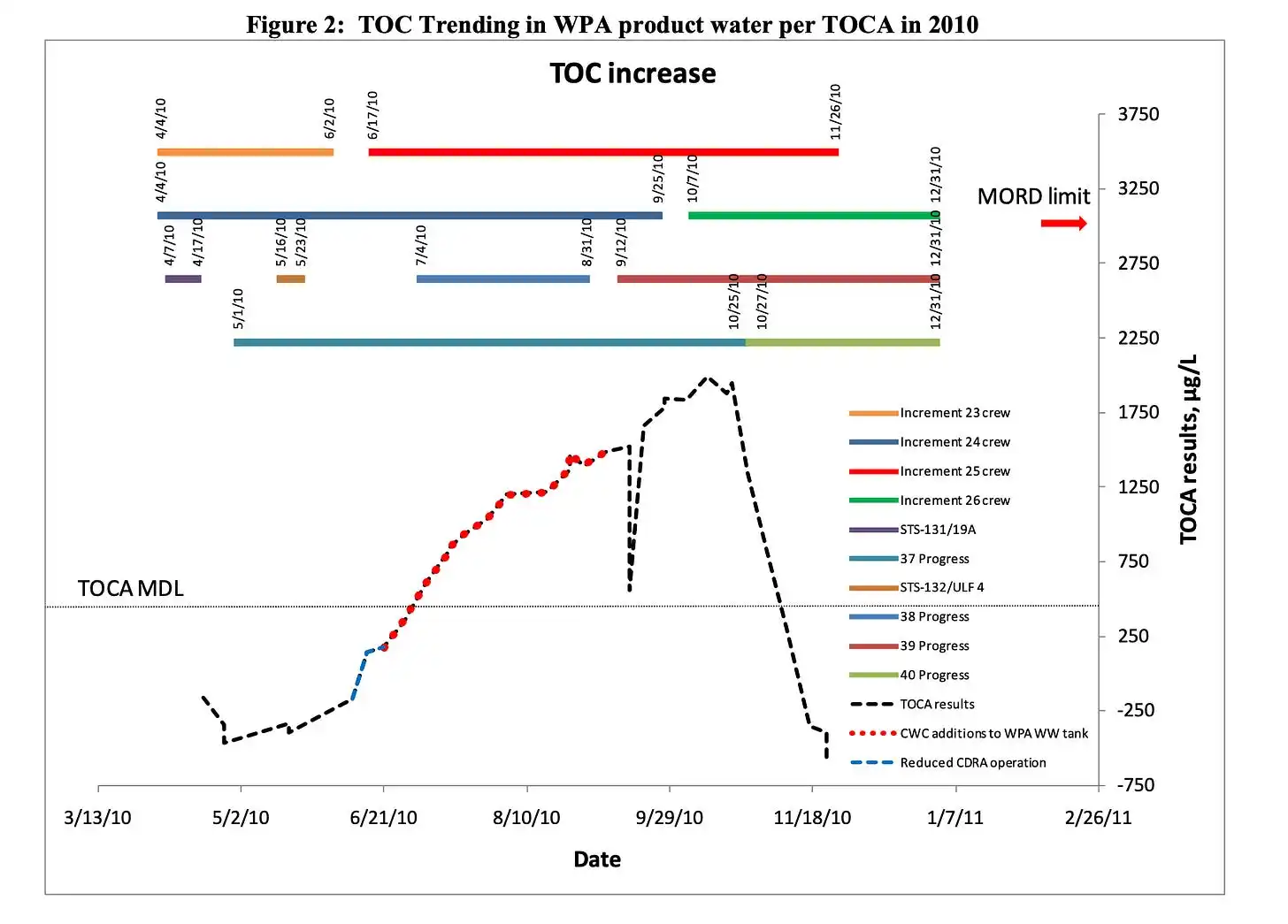
NASA's space station had a recurring problem with siloxane contamination in its water supply, which was caused by antiperspirants and other personal hygiene products. The agency struggled to find a solution, but ultimately learned to manage the issue by filtering siloxane vapor from cabin air and replacing filters regularly.
Thomas Nagel's article "What Is It Like to Be a Bat" argues that subjective experience cannot be reduced to physical explanations. He claims that understanding what it's like to be a bat requires taking up the bat's point of view.
To access academic.oup.com, check if your internet or firewall settings have blocked "challenges.cloudflare.com". Adjust settings or try a different network if necessary.
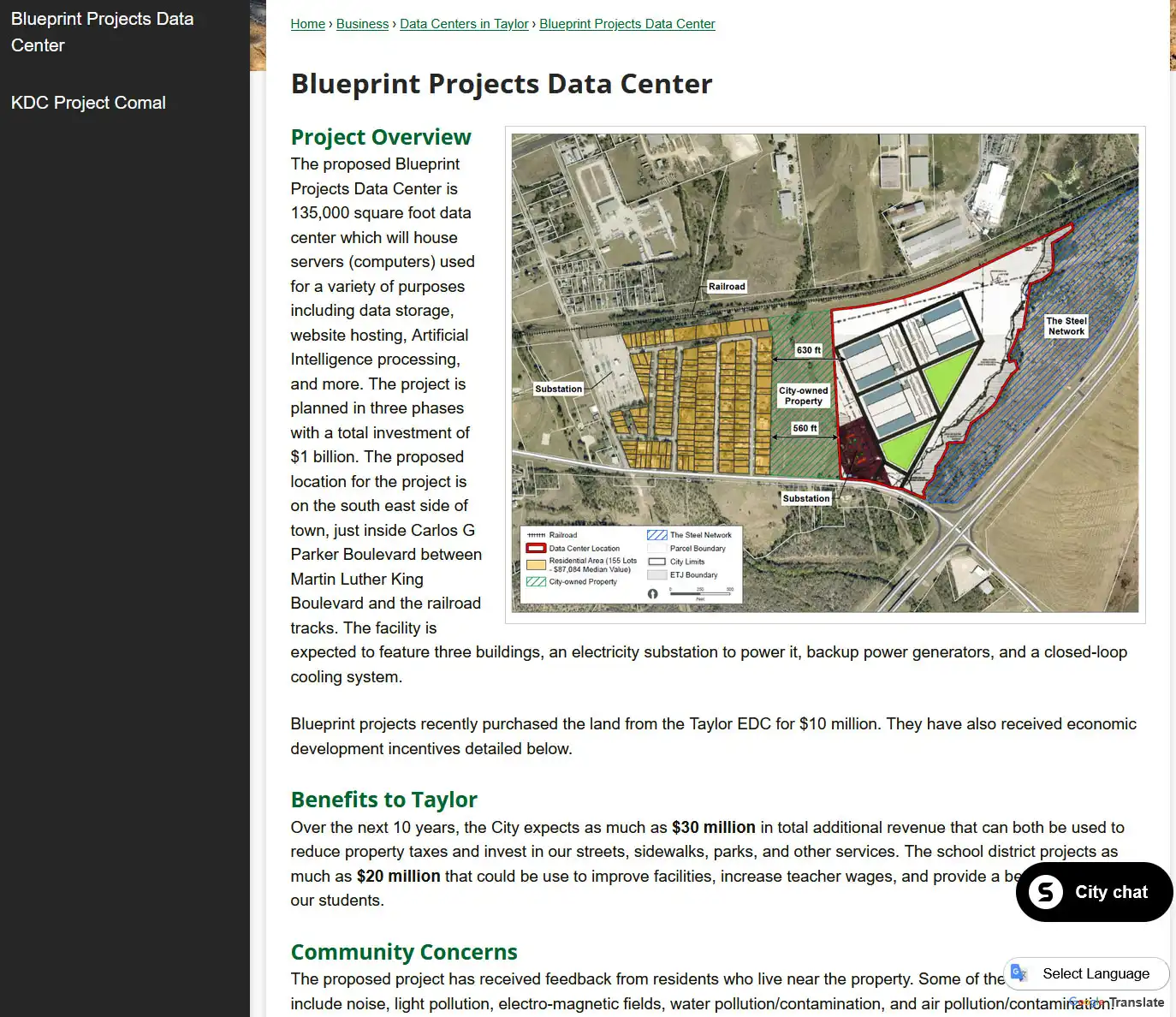
A farmer donated 87 acres of land in Taylor, Texas, to the city in 1999 for $10 with the condition it be used as a park, but it was sold to a data center developer in 2025 for $10M. Locals are fighting the development in court, citing the original deed and concerns about health risks, noise, and property values, with a decision pending in the Third Court of Appeals.
The Tyee is a successful online news outlet that relies on reader support to fund its journalism, unlike many other publications struggling with AI-driven content scraping. The Tyee is launching a spring member drive to sign up 650 new or upgraded recurring members by June 15.
A utility company's website had a big problem with a lengthy application process. The solution was to build a new version using Astro, an HTML-first approach, which doubled the company's users overnight.

I had some free time, and I noticed the 29th IOCCC started. So I decided to code an entry for the contest. If you haven't heard about the International Obfuscated C Code Contest, it is a contest running since 1984 and created by Landon Curt Noll. The objective of this contest is writing an obfuscated C program under certain size limitations specified by the rules. This year the maximum ...
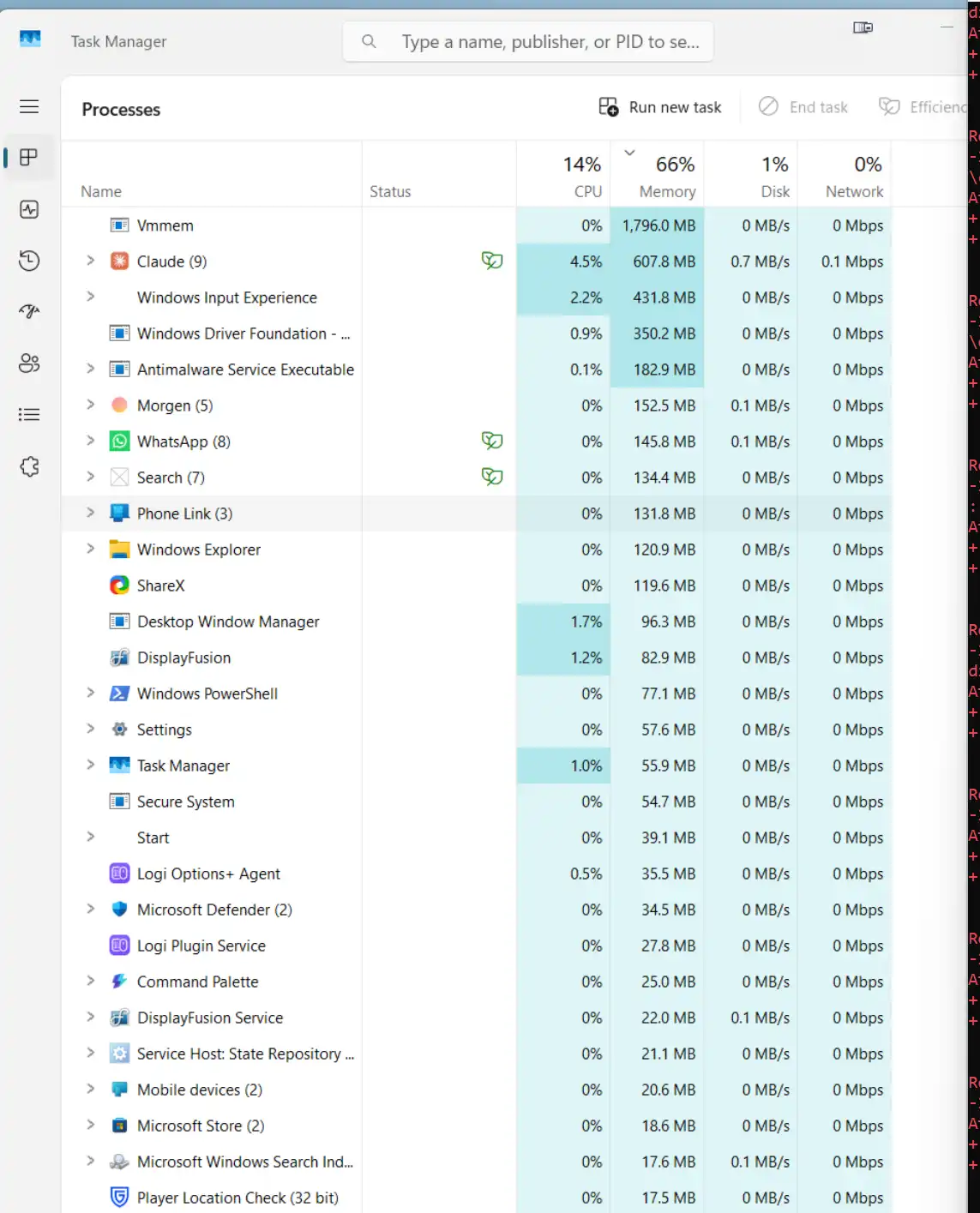
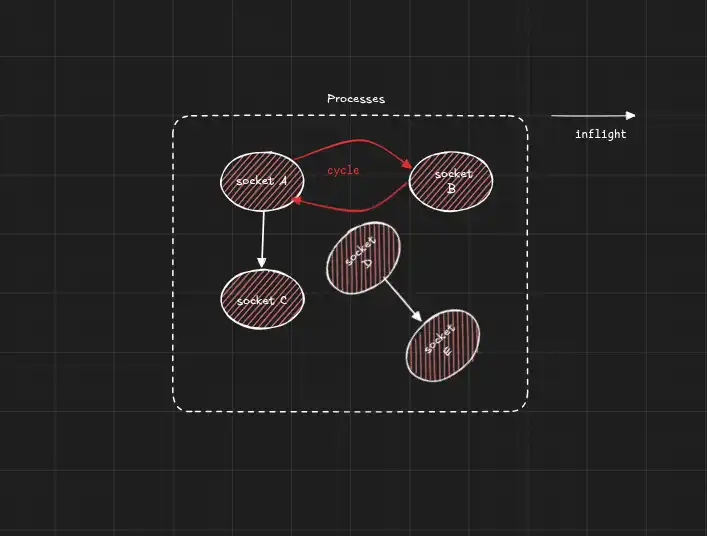
Burr is a Python framework for building AI applications with state management and debugging tools. It provides a robust framework for designing complex behaviors and is easier to use than other platforms like LangChain.
The user visited DeepSeek's HQ in Hangzhou, China, and met with their team, learning about their low-profile approach and focus on AI development without scaling up. They compared DeepSeek's AI model to others, including OpenAI and Anthropic, and found it to be more practical and cost-effective, with a sustainable pricing model that challenges the US AI giants' high markup.
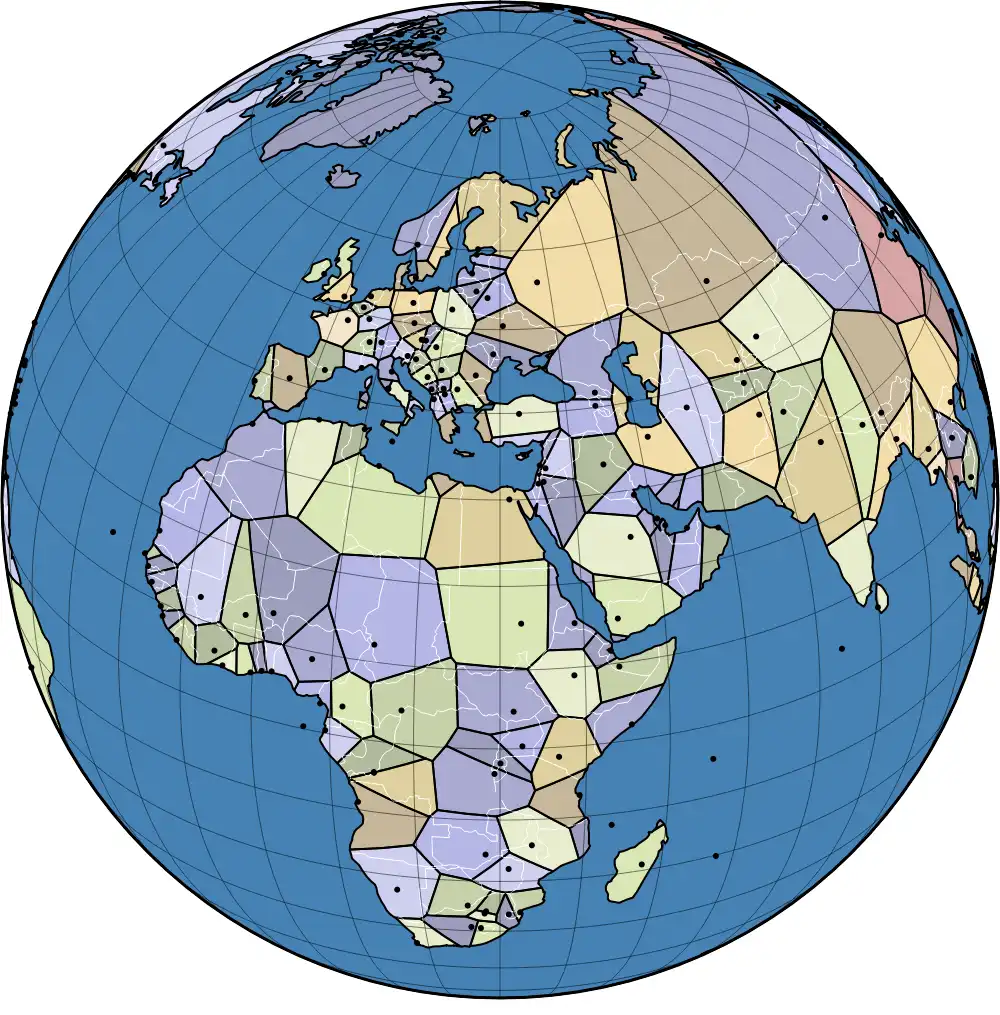
Japan's railway network expanded from a single line in 1872 to over 9,000 stations by the 21st century. The map shows stations opening over time, revealing Japan's geography through railway development.
With the release of Claude Fable, it is clear that Anthropic is progressing from poems to enterprise-scale narrative objects. To keep pace with competitors, the company is developing a broad portfolio of models optimized for the full literary stack.